Products are selected by our editors, we may earn commission from links on this page.
In 2003, a midlevel manager at the National Institute of Standards and Technology, Bill Burr, helped shape how millions of people created passwords. His eight-page guide urged users to invent complex combinations of letters, numbers, and symbols—and to change them every 90 days. The advice spread quickly across government agencies, universities, and companies. It soon became the global template for password security.
The logic seemed solid at the time. If passwords were harder to guess and changed often, hackers would struggle to break in. Burr’s guide even suggested transforming simple words into tangled strings like “pr0t3cT3d4!” The rule carried the weight of NIST’s authority, and as Professor Alan Woodward later noted, anything under the NIST banner tends to have “a long-lasting impact.”
But over time, cracks began to show. In an interview with The Wall Street Journal, Burr admitted, “Much of what I did I now regret.” Instead of improving security, the rule created predictable, weak habits. The problem was not the theory—it was how real people behaved when forced to follow it. That behavior would reshape cybersecurity advice for years to come.
“Password1” to “Password2”
When people were told to change passwords every 90 days, most did not invent entirely new ones. They made small tweaks. “Monkey1” became “Monkey2.” “Password!” became “Password2!” These minor changes were easy for attackers to predict. According to experts cited by the BBC, frequent reset demands often resulted in weaker passwords, not stronger ones.
The same pattern appeared with special characters. While the rules encouraged symbols and capital letters, many users followed similar formulas. As The Verge reported, people often relied on predictable substitutions. Hackers and automated tools quickly adapted, targeting those common patterns. What looked complex on the surface was surprisingly easy to crack.
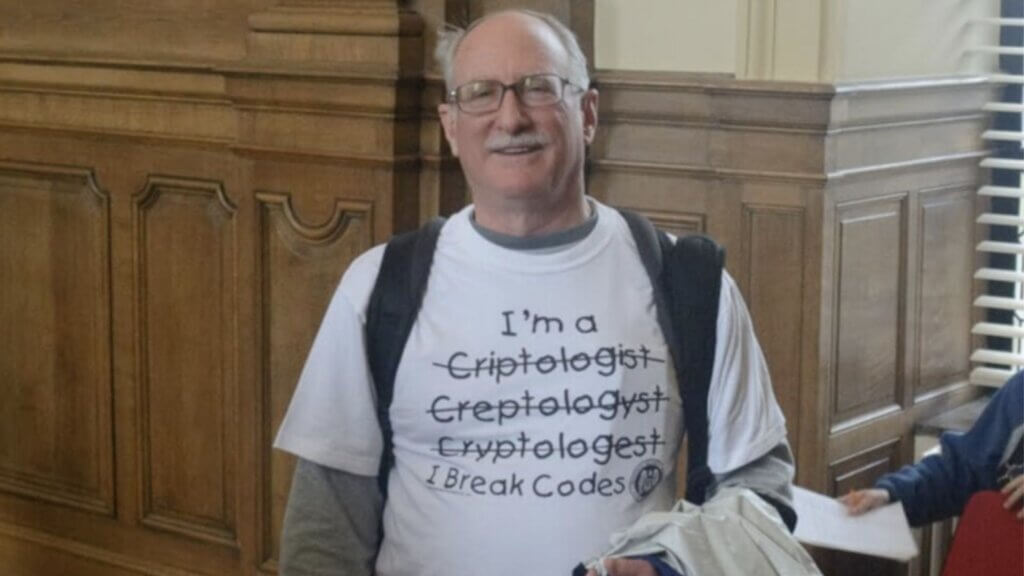
Security researchers also found something surprising: long, random word phrases like “pig coffee wandered black” could be harder for computers to break than short, scrambled passwords like “br0k3n!” The complexity people were taught to trust did not always offer real protection. The more often users were forced to reset passwords, the more careless and repetitive they became.
The Official U-Turn

Over time, NIST reconsidered its position. Adviser Paul Grassi led a two-year revision of the original standards. The agency dropped the 90-day expiration rule and removed strict requirements for special characters. Grassi said those rules “actually had a negative impact on usability.” The updated guidelines marked a major shift in official cybersecurity thinking.
Britain’s National Cyber Security Centre had already advised organizations in 2015 to abandon mandatory password resets. Instead, experts began recommending password managers—secure programs that store complex logins so users do not have to memorize them. Researchers argued that evidence, not tradition, should guide security advice.
Dr. Steven Murdoch of University College London welcomed the change, saying it was “good that password advice is now being updated to be based on evidence.” Yet he also warned that outdated advice still lingers in other areas of computer security. The story of the 90-day rule shows how even well-meaning standards can go wrong.
What We Should Be Doing Instead

Today’s guidance is simpler. Instead of frequent resets, experts recommend long, memorable passphrases. These can be easier for people to recall and harder for computers to guess. Users are now advised to change passwords only if there is evidence of a breach. The focus has shifted from forced complexity to realistic protection.
Password managers have also become central to modern security strategies. They generate unique passwords for every account and store them securely. This reduces the temptation to reuse the same login across multiple platforms, a habit that experts say greatly increases risk. Convenience, it turns out, can strengthen security when designed properly.
Bill Burr’s regret is a reminder that technology advice evolves. What once seemed like common sense led to habits that weakened defenses. By learning from those mistakes, cybersecurity experts now promote solutions rooted in real human behavior. The lesson is clear: the strongest security rules must work with people, not against them.
